The New Year is a great time to take inventory of your online security setup.
We can’t control the (now commonplace) security breaches at companies that hold our data, but we can ensure that we don’t have any glaring holes that would make us an easy, vulnerable target.
It’s Not Just About Passwords
We’ll get to strong passwords in a minute, but by now I hope we’ve all learned that passwords alone can’t fully protect us. Here are a few things that can help offer additional layers of protection.
Things to Do Right Now
- Two-Factor Authentication – This is probably the most powerful and easiest security feature to turn on. Every major social network and credible banking system will have this feature which requires two things to login – your password and a second physical thing like a text message, device, or fingerprint.
- Avoid Debit Cards – If someone steals your credit card, you can simply decline false charges and not pay them. But if someone steals your debit card, the money they use is gone and much harder to get back. Racking up debt with a credit card is bad, but if you use your money wisely to begin with, then you’re safe with a credit card.
Things to Consider
- One-Time Credit Card Numbers – Bank of America, Citi, and others allow you to generate a one-time use (or multiple use with an expiration date) credit card number you can use for online transactions. For sites you plan to only use once this can be great. However, you might avoid it if you think you’ll return the item or if you’re reserving a hotel or rental card where you need to show the card in person to verify.
- Alternate Email Addresses – For a long time, I’ve used a common email address across a lot of accounts, but based on the recommendations I’m seeing creating additional less public emails for networks can make it harder to link all of a person’s accounts or use those addresses for phishing attacks.
- Alternate Phone Numbers – Again, listing the same phone number publicly in several accounts makes that number less secure. Having a secondary, less public number like a Google Voice account that you use for Two-Factor can strengthen your overall security.
Good Passwords Are Strong and Unique
What undergirds all the practices above is having a good system of passwords, and that means they need to be both strong and unique.
- Strong passwords – A strong password is one that can’t be easily guessed by a machine, and a password becomes stronger when it either uses more characters (not just the 26 lowercase letters, but also uppercase, numbers, and symbols), or is very long, or both.
- Unique passwords – Even if you have the strongest password in the world, if you use it for Facebook, your bank, and your email, once that password is lost, you’ll be out of luck.
One of the best ways to ensure that you have strong, unique passwords for each website or service is to turn off your browser’s default username/password use a tool like 1Password or KeePass. These tools can generate very strong passwords and manage them for you across websites and browsers.
The Problem with “Strong Passwords”
Even if you use 1Password, KeePass, or another tool, you still need at least one good, strong master password that’s not written down anywhere and isn’t recorded in another electronic tool. Further, whether or not you use a manager, the password requirements for many websites can sometimes cause more problems than they solve. Most websites attempt to help you create a strong password by requiring that your password meet the following criteria:
- 8 or more characters
- Upper and lowercase
- At least one number
- At least one symbol
In theory, these requirements are a great way to force people to make strong passwords. However, in practice, the past few decades have shown that there are several problems with these 8-letter strong passwords:
- It’s hard for humans to remember a truly random set of characters, so we often take a common word and replace a few letter with symbols (a => @, s => $).
- Because even that is hard to remember, we use the same password for dozens of websites and that makes us vulnerable.
- An 8 character password that meets the above requirements is actually not as secure as a longer password with all lowercase letters.
On the last point, this brilliant XKCD comic points out the vast security difference between a short “complex” password and a longer “simple” password
- Tr0ub4or&3 = 28 bits of entropy, 3 days for computer to guess (1000/sec)
- correcthorsebatterystaple = 44 bits of entropy, 550 years for a computer to guess
It turns out that 24 letters instead of 10 letters – even without uppercase, number, or symbols – is much, much more secure. And, it’s way easier to remember.
The problem is that many websites won’t let you make passwords like “ilovejesusandpumpkinpie” even if it is several orders of magnitude more secure because they still require uppercase letters, numbers, and symbols.
The Bible as a Strong Password Generator
So here’s a fun solution that can meet both the requirements of websites and manage to be more secure: A Bible reference.
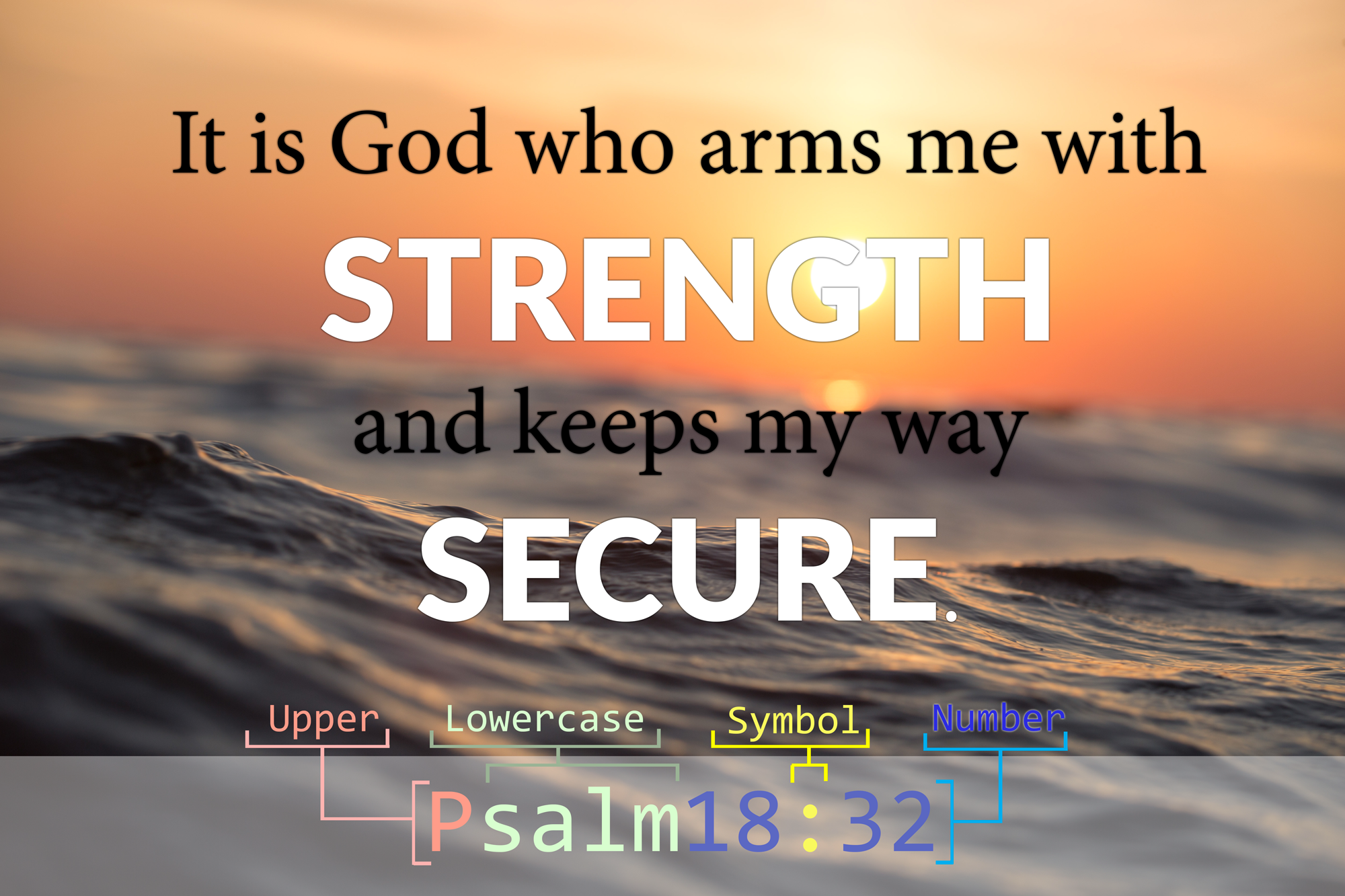
Take a look at the following well-known reference:
John3:16
It has (1) upper and (2) lowercase letters, (3) numbers, and (4) a symbol (see opening graphic). This means it (1) meets most password security requirements, and (2) it’s easy to remember.
You can have lots of fun thinking of references that are little inside jokes to yourself, such as “1Chronicles4:10” (for your bank) or “Leviticus3:16” (for your fitness tracker) or “Exodus34:35” (for Facebook).
But, there are two important caveats. First, common references like “John3:16” are probably the “password123” of bad Christian passwords, and the ones I mentioned above might be overused due to their inherent hilarity. So please you avoid using anything that’s ever been written on Tim Tebow’s face or turned into a multi-million dollar empire.
Second, as some commenters pointed out (thanks fellas!), it is possible that someone could attempt to hack passwords that fit the Bible verse pattern, so it’d be best to also include a random word or two that will both lengthen the password and increase its overall entropy/security.
John3:16 – meets password standards, but is still hackable
John3:16pumpkinroof – meets password standards, plus more entropy
In summary, it’s always best to use long, random passwords from a generator, but for this few that you need to remember yourself, if you can meaningful but uncommon references and add one or two random words to it, then combined with the security practices above, you should be well on your way to a more secure 2017.
Special thanks to Robert Estienne for inventing the modern versification system 🙂

Woah, how are Bible verses at all secure? Wouldn’t it be trival to brute force? $Book$Number:$Number where $number iterates through spellings as well. That seems incredinly low entropy, a really bad idea for passwords because it follows a pattern that’s way too easy tk iterate through.
The reason crazy horse staple battery works is because it’s being multiplied by the entire size of the English dictionary four times — it’s exponentially more complicated. A Bible password like you suggest only contains a few variables with a short set of possible values.
For stupid bank passwords, I’d go total random stting with maximum complexity and a password manager.
I’m sorry brother, but this is not a very good plan. Even if you figure deuterocanonical books so you have more than 66 book names to work with you are working with a very limited set of values. The set of all bible book names, chapters, and verses is very very small (to a computer). Factor in spelling out or not spelling out every chapter and/or verse reference and optionally capitalizing bits, you still have a VERY small entropy pool.
It’s better than password123 or your zip code, but adding this idea to a cracking library will slow a brute force routine by less time than its taking me to write this comment. Having all the _elements_ of a good password is only half the battle, without entropy you’re trying to buy a stairway to heaven.
`correcthorsebatterystable` … Oops!! 😉
Of course, I’d rather have a “stable battery” than a “battery staple” too, but that’s not what Randall Munroe thought.
Whoops! Fixed — thanks!
@Blaise and @Caleb, thanks for pointing that out. Reading back through it, I didn’t make it clear that you shouldn’t use the reference alone, but should add a word or two to the reference. I’ve gone back and edited the post to make that more clear.
Great article John. I’m now thinking I should get rid of debit cards and get a single credit card. I enjoyed reading the article.
John, thanks for the great post and tips for helping everyone secure up their information. I was surprised about your advice on ‘Avoid Debit Cards’ because it contradicted what I thought about the topic. I’m pretty sure you have the same options to dispute debit card purchases as you would your credit card. You’re protected in cases of fraud no matter what, though in the case of a debit card, you cash on hand is affected until the disputed charges are resolved. I would recommend doing research on the Federal Reserve’s Regulation E.
Ben, yes I avoid debit cards for exactly the reason you mention – that your cash is affected until the complaint is resolved. It’s not just not a risk I want to take.